Create and Configure the VM-Series Firewall
Table of Contents
10.0 (EoL)
Expand all | Collapse all
-
- VM-Series Deployments
- VM-Series in High Availability
- Enable Jumbo Frames on the VM-Series Firewall
- Hypervisor Assigned MAC Addresses
- Custom PAN-OS Metrics Published for Monitoring
- Interface Used for Accessing External Services on the VM-Series Firewall
- PacketMMAP and DPDK Driver Support
- Enable ZRAM on the VM-Series Firewall
-
- VM-Series Firewall Licensing
- Create a Support Account
- Serial Number and CPU ID Format for the VM-Series Firewall
- Install a License API Key
- Use Panorama-Based Software Firewall License Management
-
- Maximum Limits Based on Memory
- Activate Credits
- Create a Deployment Profile
- Manage a Deployment Profile
- Register the VM-Series Firewall (Software NGFW Credits)
- Provision Panorama
- Migrate Panorama to a FW-Flex License
- Transfer Credits
- Renew Your Software NGFW Credit License
- Deactivate License (Software NGFW Credits)
- Create and Apply a Subscription-Only Auth Code
- Migrate to a Flexible VM-Series License
- What Happens When Licenses Expire?
-
- Supported Deployments on VMware vSphere Hypervisor (ESXi)
-
- Plan the Interfaces for the VM-Series for ESXi
- Provision the VM-Series Firewall on an ESXi Server
- Perform Initial Configuration on the VM-Series on ESXi
- Add Additional Disk Space to the VM-Series Firewall
- Use VMware Tools on the VM-Series Firewall on ESXi and vCloud Air
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Use the VM-Series CLI to Swap the Management Interface on ESXi
-
-
- VM-Series Firewall for NSX-V Deployment Checklist
- Install the VMware NSX Plugin
- Apply Security Policies to the VM-Series Firewall
- Steer Traffic from Guests that are not Running VMware Tools
- Dynamically Quarantine Infected Guests
- Migrate Operations-Centric Configuration to Security-Centric Configuration
- Add a New Host to Your NSX-V Deployment
- Use Case: Shared Compute Infrastructure and Shared Security Policies
- Use Case: Shared Security Policies on Dedicated Compute Infrastructure
- Dynamic Address Groups—Information Relay from NSX-V Manager to Panorama
-
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (North-South)
- Components of the VM-Series Firewall on NSX-T (North-South)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Deploy the VM-Series Firewall
- Direct Traffic to the VM-Series Firewall
- Apply Security Policy to the VM-Series Firewall on NSX-T
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Extend Security Policy from NSX-V to NSX-T
-
- Components of the VM-Series Firewall on NSX-T (East-West)
- VM-Series Firewall on NSX-T (East-West) Integration
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (East-West)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Launch the VM-Series Firewall on NSX-T (East-West)
- Add a Service Chain
- Direct Traffic to the VM-Series Firewall
- Apply Security Policies to the VM-Series Firewall on NSX-T (East-West)
- Use vMotion to Move the VM-Series Firewall Between Hosts
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Launch the VM-Series Firewall on NSX-T (East-West)
- Create Dynamic Address Groups
- Create Dynamic Address Group Membership Criteria
- Generate Steering Policy
- Generate Steering Rules
- Delete a Service Definition from Panorama
- Migrate from VM-Series on NSX-T Operation to Security Centric Deployment
- Extend Security Policy from NSX-V to NSX-T
- Use In-Place Migration to Move Your VM-Series from NSX-V to NSX-T
- Use Migration Coordinator to Move Your VM-Series from NSX-V to NSX-T
-
-
- Deployments Supported on AWS
-
- Planning Worksheet for the VM-Series in the AWS VPC
- Launch the VM-Series Firewall on AWS
- Launch the VM-Series Firewall on AWS Outpost
- Create a Custom Amazon Machine Image (AMI)
- Encrypt EBS Volume for the VM-Series Firewall on AWS
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable CloudWatch Monitoring on the VM-Series Firewall
-
- Use Case: Secure the EC2 Instances in the AWS Cloud
- Use Case: Use Dynamic Address Groups to Secure New EC2 Instances within the VPC
-
-
- What Components Does the VM-Series Auto Scaling Template for AWS (v2.0) Leverage?
- How Does the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1) Enable Dynamic Scaling?
- Plan the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1)
- Customize the Firewall Template Before Launch (v2.0 and v2.1)
- Launch the VM-Series Auto Scaling Template for AWS (v2.0)
- SQS Messaging Between the Application Template and Firewall Template
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.0)
- Modify Administrative Account and Update Stack (v2.0)
-
- Launch the Firewall Template (v2.1)
- Launch the Application Template (v2.1)
- Create a Custom Amazon Machine Image (v2.1)
- VM-Series Auto Scaling Template Cleanup (v2.1)
- SQS Messaging Between the Application Template and Firewall Template (v2.1)
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.1)
- Modify Administrative Account (v2.1)
- Change Scaling Parameters and CloudWatch Metrics (v2.1)
-
-
- Enable the Use of a SCSI Controller
- Verify PCI-ID for Ordering of Network Interfaces on the VM-Series Firewall
-
- Deployments Supported on Azure
- Deploy the VM-Series Firewall from the Azure Marketplace (Solution Template)
- Deploy the VM-Series Firewall from the Azure China Marketplace (Solution Template)
- Create a Custom VM-Series Image for Azure
- Deploy the VM-Series Firewall on Azure Stack
- Enable Azure Application Insights on the VM-Series Firewall
- Set up Active/Passive HA on Azure
- Use the ARM Template to Deploy the VM-Series Firewall
-
- About the VM-Series Firewall on Google Cloud Platform
- Supported Deployments on Google Cloud Platform
- Prepare to Set Up VM-Series Firewalls on Google Public Cloud
- Create a Custom VM-Series Firewall Image for Google Cloud Platform
-
- Deploy the VM-Series Firewall from Google Cloud Platform Marketplace
- Management Interface Swap for Google Cloud Platform Load Balancing
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable Google Stackdriver Monitoring on the VM Series Firewall
- Enable VM Monitoring to Track VM Changes on Google Cloud Platform (GCP)
- Use Dynamic Address Groups to Secure Instances Within the VPC
- Use Custom Templates or the gcloud CLI to Deploy the VM-Series Firewall
-
- Prepare Your ACI Environment for Integration
-
-
- Create a Virtual Router and Security Zone
- Configure the Network Interfaces
- Configure a Static Default Route
- Create Address Objects for the EPGs
- Create Security Policy Rules
- Create a VLAN Pool and Domain
- Configure an Interface Policy for LLDP and LACP for East-West Traffic
- Establish the Connection Between the Firewall and ACI Fabric
- Create a VRF and Bridge Domain
- Create an L4-L7 Device
- Create a Policy-Based Redirect
- Create and Apply a Service Graph Template
-
- Create a VLAN Pool and External Routed Domain
- Configure an Interface Policy for LLDP and LACP for North-South Traffic
- Create an External Routed Network
- Configure Subnets to Advertise to the External Firewall
- Create an Outbound Contract
- Create an Inbound Web Contract
- Apply Outbound and Inbound Contracts to the EPGs
- Create a Virtual Router and Security Zone for North-South Traffic
- Configure the Network Interfaces
- Configure Route Redistribution and OSPF
- Configure NAT for External Connections
-
-
- Choose a Bootstrap Method
- VM-Series Firewall Bootstrap Workflow
- Bootstrap Package
- Bootstrap Configuration Files
- Generate the VM Auth Key on Panorama
- Create the bootstrap.xml File
- Prepare the Licenses for Bootstrapping
- Prepare the Bootstrap Package
- Bootstrap the VM-Series Firewall on AWS
- Bootstrap the VM-Series Firewall on Azure
- Bootstrap the VM-Series Firewall on Google Cloud Platform
- Verify Bootstrap Completion
- Bootstrap Errors
End-of-Life (EoL)
Create and Configure the VM-Series Firewall
Learn how to create a VM-Series instance in Alibaba Cloud,
and create the network interfaces for the VM-Series firewall.
This task uses the ECS console to create a
VM-Series firewall instance with a minimum of three interfaces:
management, untrust, and trust. An ECS instance supports a single
NIC by default, and automatically attaches an Elastic Network Interface
(ENI) to it. To support the VM-Series firewall, you must separately
create the Untrust and Trust Elastic Network Interfaces (ENIs) and
attach them to your instance.
- From the Alibaba Cloud console home page, select Elastic Compute ServiceInstances & ImagesInstances, and click Create Instance on the upper right.
- Select Custom Launch.
- Basic Configurations.
- Fill in the following values. For example:
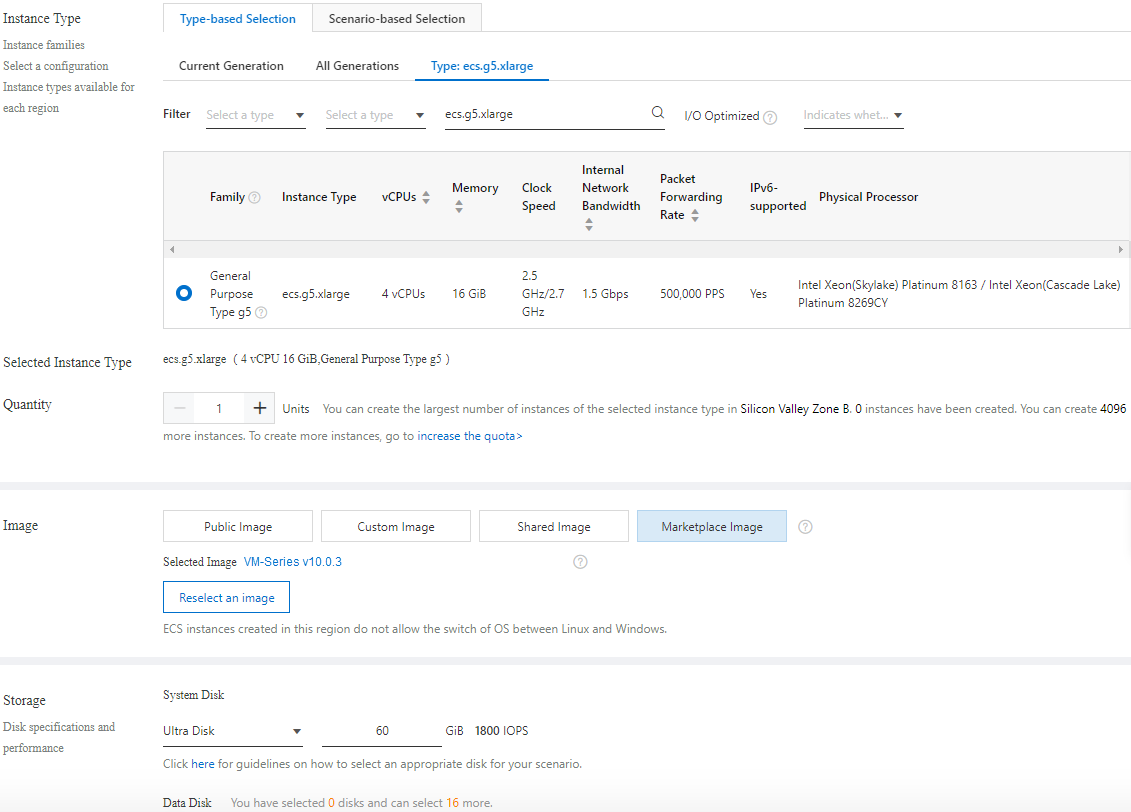
Property Value Billing Method Subscription. Region Your choice. You can also select a Zone. The region you select must provide one of the required instance types. Instance Type One of the types in Alibaba Cloud Instance Type Recommendations for the VM-Series Firewall. You can use Type-based Selection to search for the instance type. Image Select Marketplace Image and search the Alibaba Marketplace for “VM-Series”. The image combines the OS and the VM-Series firewall. Storage Choose a disk type and specify 60 GB. Snapshot Your choice. Duration Your choice. ![]()
- Select Next: Networking.
- Fill in the following values. For example:
- On the Networking page, supply the following values.
- Network (select VPC).
- Choose the VPC you created in Create a VPC and Configure Networks.
- Choose the Management VSwitch.
- Public IP Address.If you do not have a public IP address, enable Assign Public IP address and the system will allocate one. If you must use a specific IP address, or an address in a specific range, you can request a custom IP address. Refer to the Elastic IP Address User Guide.
- Security Group.Select the Management security group.
- Elastic Network Interface.The Management interface is already attached to eth0.
- Select Next: System Configurations.
- Network (select VPC).
- On the System Configurations page, fill in the following
values.
- Logon Credentials: Select Key
Pair. Password authentication is not supported.
- Name the VM-Series firewall instance and supply a
Host name.Make any corrections.Select Preview to view your settings thus far.
- Following Advanced (based or instance RAM
roles or cloud-init) click Show.
- The RAM role is optional.
- In the User Data field, enter basic bootstrap information as key-value pairs separated by newlines. See Enter a Basic Configuration as User Data (Public Clouds). For example, enter the following in the User Data field.
type=dhcp-client hostname=Ca-FW-DC1 vm-auth-key=7550362253**** panorama-server=10.*.*.20 panorama-server-2=10.*.*.21 tplname=FINANCE_TG4 dgname=finance_dg op-cmd-dpdk-pkt-io=on dhcp-send-hostname=yes dhcp-send-client-id=yes dhcp-accept-server-hostname=yes dhcp-accept-server-domain=yes authcodes=I7115398 vm-series-auto-registration-pin-id=abcdefgh1234**** vm-series-auto-registration-pin-value=zyxwvut-0987****
op-command-modes (mgmt-interface-swap and jumbo frame) are not supported for Alibaba Cloud.op-cmd-dpdk-pkt-io=on supports DPDK. If you want to specify PacketMMAP, specify op-cmd-dpdk-pkt-io=offGrouping is Optional. Select Preview to view the configuration before ordering.
- Logon Credentials: Select Key
Pair.
- View the terms of service, and select Create
Order to create the VM-Series firewall instance.View the purchase order and select Subscribe.
- From the console home page, choose Elastic Compute ServiceNetworks
and SecurityENIs and
select Create ENI in the top right corner. Create
elastic network interfaces for the Untrust and Trust interfaces.
- Create the Untrust ENI. In the Actions column, select Bind to Instance and select the instance you just created.
- Create the Trust ENI and bind it to the instance.
- Create the Untrust ENI.
- Allocate Elastic IP (EIP) addresses.Allocate EIP addresses for the VM-Series firewall Management interface and the Untrust network interface. In this example the Trust interface is not exposed to the internet, so you don’t need a third IP address.If you already have two EIPs, go to the next step.
- Associate an EIP with the VM-Series firewall Management interface.
- Associate an EIP with the VM-Series firewall Untrust
network interface.The second interface you attach is assigned to network interface 1 on the VM-Series firewall.
- Restart your instance to attach the new network interfaces.On the Instances list, select your instance, select Manage, and select Restart on the upper right.
- SSH in
to the VM-Series firewall with the security key and set the admin
password:
developer1$ ssh -i dev1-vpc1.pem admin@18.***.145.153 Welcome admin. admin> configure Entering configuration mode [edit] admin# set mgt-config users admin password Enter password:<password> Confirm password:<password> [edit] admin# commit
- Access the VM-Series firewall web interface.Open a web browser and enter the EIP for the management interface.