Download PDF
GlobalProtect
Manually Add and Delete Devices From the Quarantine List
Table of Contents
Expand All
|
Collapse All
GlobalProtect Docs
-
10.1 & Later
- 10.1 & Later
- 9.1 (EoL)
-
- How Does the App Know Which Certificate to Supply?
- Set Up Cloud Identity Engine Authentication
- Configure GlobalProtect to Facilitate Multi-Factor Authentication Notifications
- Enable Delivery of VSAs to a RADIUS Server
- Enable Group Mapping
-
-
- GlobalProtect App Minimum Hardware Requirements
- Download the GlobalProtect App Software Package for Hosting on the Portal
- Host App Updates on the Portal
- Host App Updates on a Web Server
- Test the App Installation
- Download and Install the GlobalProtect Mobile App
- View and Collect GlobalProtect App Logs
-
-
- Deploy App Settings in the Windows Registry
- Deploy App Settings from Msiexec
- Deploy Scripts Using the Windows Registry
- Deploy Scripts Using Msiexec
- Deploy Connect Before Logon Settings in the Windows Registry
- Deploy GlobalProtect Credential Provider Settings in the Windows Registry
- SSO Wrapping for Third-Party Credential Providers on Windows Endpoints
- Enable SSO Wrapping for Third-Party Credentials with the Windows Registry
- Enable SSO Wrapping for Third-Party Credentials with the Windows Installer
- Deploy App Settings to Linux Endpoints
- GlobalProtect Processes to be Whitelisted on EDR Deployments
-
-
- Mobile Device Management Overview
- Set Up the MDM Integration With GlobalProtect
- Qualified MDM Vendors
-
-
- Set Up the Microsoft Intune Environment for Android Endpoints
- Deploy the GlobalProtect App on Android Endpoints Using Microsoft Intune
- Create an App Configuration on Android Endpoints Using Microsoft Intune
- Configure Lockdown Mode for Always On Connect Method on Android Endpoints Using Microsoft Intune
-
- Deploy the GlobalProtect Mobile App Using Microsoft Intune
- Configure an Always On VPN Configuration for iOS Endpoints Using Microsoft Intune
- Configure a User-Initiated Remote Access VPN Configuration for iOS Endpoints Using Microsoft Intune
- Configure a Per-App VPN Configuration for iOS Endpoints Using Microsoft Intune
-
-
-
- Create a Smart Computer Group for GlobalProtect App Deployment
- Create a Single Configuration Profile for the GlobalProtect App for macOS
- Deploy the GlobalProtect Mobile App for macOS Using Jamf Pro
-
- Enable GlobalProtect System Extensions on macOS Endpoints Using Jamf Pro
- Enable GlobalProtect Network Extensions on macOS Big Sur Endpoints Using Jamf Pro
- Add a Configuration Profile for the GlobalProtect Enforcer by Using Jamf Pro 10.26.0
- Verify Configuration Profiles Deployed by Jamf Pro
- Remove System Extensions on macOS Monterey Endpoints Using Jamf Pro
- Non-Removable System Extensions on macOS Sequoia Endpoints Using Jamf Pro
- Uninstall the GlobalProtect Mobile App Using Jamf Pro
-
- Configure HIP-Based Policy Enforcement
- Configure HIP Exceptions for Patch Management
- Collect Application and Process Data From Endpoints
- Redistribute HIP Reports
-
- Identification and Quarantine of Compromised Devices Overview and License Requirements
- View Quarantined Device Information
- Manually Add and Delete Devices From the Quarantine List
- Automatically Quarantine a Device
- Use GlobalProtect and Security Policies to Block Access to Quarantined Devices
- Redistribute Device Quarantine Information from Panorama
- Troubleshoot HIP Issues
-
-
- Enable and Verify FIPS-CC Mode on Windows Endpoints
- Enable and Verify FIPS-CC Mode on macOS Endpoints
- Enable and Verify FIPS-CC Mode Using Workspace ONE on iOS Endpoints
- Enable FIPS Mode on Linux EndPoints with Ubuntu or RHEL
- Enable and Verify FIPS-CC Mode Using Microsoft Intune on Android Endpoints
- FIPS-CC Security Functions
- Resolve FIPS-CC Mode Issues
-
-
- Remote Access VPN (Authentication Profile)
- Remote Access VPN (Certificate Profile)
- Remote Access VPN with Two-Factor Authentication
- GlobalProtect Always On VPN Configuration
- Remote Access VPN with Pre-Logon
- User-Initiated Pre-Logon Connection
- GlobalProtect Multiple Gateway Configuration
- GlobalProtect for Internal HIP Checking and User-Based Access
- Mixed Internal and External Gateway Configuration
- Captive Portal and Enforce GlobalProtect for Network Access
- GlobalProtect on Windows 365 Cloud PC
-
- About GlobalProtect Cipher Selection
- Cipher Exchange Between the GlobalProtect App and Gateway
-
- Reference: GlobalProtect App Cryptographic Functions
-
- Reference: TLS Ciphers Supported by GlobalProtect Apps on macOS Endpoints
- Reference: TLS Ciphers Supported by GlobalProtect Apps on Windows Endpoints
- Reference: TLS Ciphers Supported by GlobalProtect Apps on Android 6.0.1 Endpoints
- Reference: TLS Ciphers Supported by GlobalProtect Apps on iOS 10.2.1 Endpoints
- Reference: TLS Ciphers Supported by GlobalProtect Apps on Chromebooks
- Ciphers Used to Set Up IPsec Tunnels
- SSL APIs
-
- View a Graphical Display of GlobalProtect User Activity in PAN-OS
- View All GlobalProtect Logs on a Dedicated Page in PAN-OS
- Event Descriptions for the GlobalProtect Logs in PAN-OS
- Filter GlobalProtect Logs for Gateway Latency in PAN-OS
- Restrict Access to GlobalProtect Logs in PAN-OS
- Forward GlobalProtect Logs to an External Service in PAN-OS
- Configure Custom Reports for GlobalProtect in PAN-OS
-
6.3
- 6.3
- 6.2
- 6.1
- 6.0
- 5.1
-
- Download and Install the GlobalProtect App for Windows
- Use Connect Before Logon
- Use Single Sign-On for Smart Card Authentication
- Use the GlobalProtect App for Windows
- Report an Issue From the GlobalProtect App for Windows
- Disconnect the GlobalProtect App for Windows
- Uninstall the GlobalProtect App for Windows
- Fix a Microsoft Installer Conflict
-
- Download and Install the GlobalProtect App for macOS
- Use the GlobalProtect App for macOS
- Report an Issue From the GlobalProtect App for macOS
- Disconnect the GlobalProtect App for macOS
- Uninstall the GlobalProtect App for macOS
- Remove the GlobalProtect Enforcer Kernel Extension
- Enable the GlobalProtect App for macOS to Use Client Certificates for Authentication
-
6.1
- 6.1
- 6.0
- 5.1
-
6.3
- 6.3
- 6.2
- 6.1
- 6.0
- 5.1
Manually Add and Delete Devices From the Quarantine List
Learn how to manually add devices to the quarantine list from various pages or logs
or using the Host ID to identify the device.
You can add a device manually from either
the quarantine pages, from the GlobalProtect, Threat, Traffic, or Unified logs, or by using
an API. You can also manually delete the device from the quarantine
pages, as shown in the following steps.
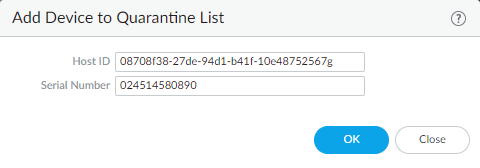
- To manually add a device to the quarantine list from the Device Quarantine page, select DeviceDevice Quarantine or PanoramaDevice Quarantine and Add the device.Add the Host ID and, optionally, the Serial Number of the device. GlobalProtect uses the Host ID to identify the device.

- To add a device to the quarantine list from the GlobalProtect, Threat, Traffic, or Unified logs, complete the following steps.
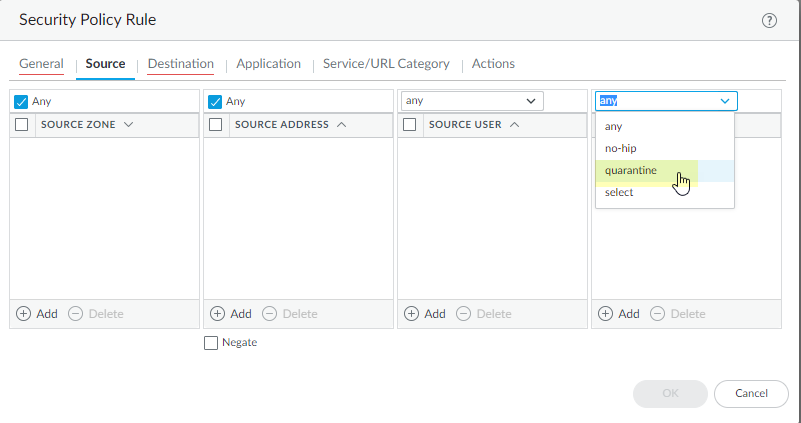
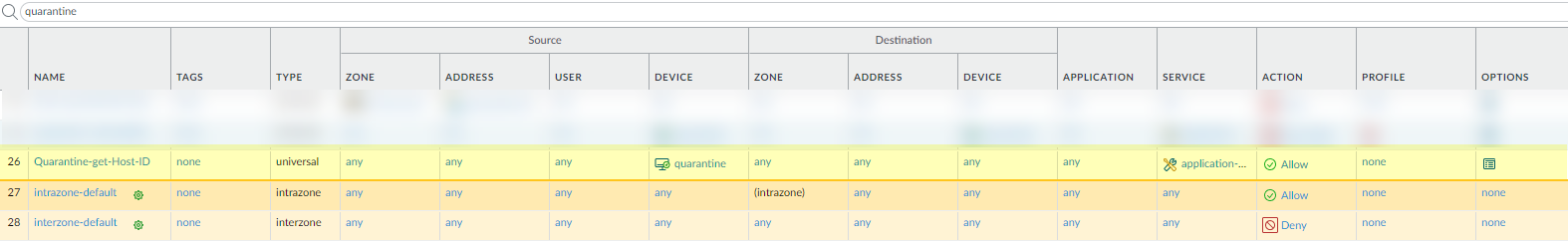
- (Threat, Traffic, and Unified Logs Only) To add Host ID information to the Traffic, Threat, and Unified logs, select PoliciesSecurity and Add a security policy rule; then, select Quarantine as the Source Device for Source traffic.A Host ID is required to add a device to the quarantine list. When a user connects to the network with the GlobalProtect app, GlobalProtect automatically adds Host ID information for the connected endpoint to the GlobalProtect log. The host ID value varies by endpoint type:
- Windows—Machine GUID stored in the Windows registry (HKEY_Local_Machine\Software\Microsoft\Cryptography\MachineGuid)
- macOS—MAC address of the first built-in physical network interface
- Android—Android ID
- iOS—UDID
- Chrome—GlobalProtect assigned unique alphanumeric string with length of 32 characters.
If you do not know the host ID, you can correlate the user-ID to the host ID in the HIP Match logs:- Select MonitorLogsHIP Match.
- Filter the HIP match logs for the source user associated with the endpoint.
- Open the HIP match log and identify the host ID under OSHost ID and optionally the hostname under Host InformationMachine Name.
For GlobalProtect to automatically add Host ID information to the Traffic, Threat, or Unified logs, you must add a policy rule that has Quarantine selected for source traffic. To make sure that you are adding the Host ID for all devices you want to quarantine (either manually or automatically), create a security policy that allows all traffic and specify Quarantine as the Source Device. It does not matter what order you place this policy in the list of policies for it to work.
To make sure that you are adding the Host ID for all devices you want to quarantine (either manually or automatically), create a security policy that allows all traffic and specify Quarantine as the Source Device. It does not matter what order you place this policy in the list of policies for it to work.
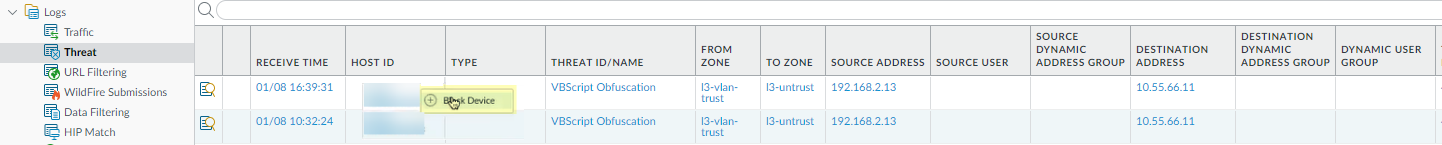
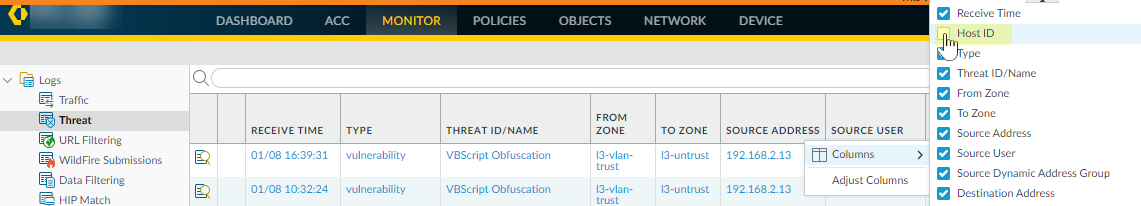
- Right-click the Host ID associated with the device and click Block Device.
 If the Host ID column does not display, select the header of any column and then select the Host ID field to display the Host ID.
If the Host ID column does not display, select the header of any column and then select the Host ID field to display the Host ID.
- To create an API to manually add the devices, see the instructions in the PAN-OS and Panorama API Usage Guide.
- After your administrator has performed remediation on the device, you can delete it from the list by selecting DeviceDevice Quarantine for next-generation firewalls or PanoramaDevice Quarantine for Panorama appliances, selecting one or more devices, then selecting Delete.