GlobalProtect
Redistribute HIP Reports
Table of Contents
Expand All
|
Collapse All
GlobalProtect Docs
-
- 10.1 & Later
- 9.1 (EoL)
-
- 6.3
- 6.2
- 6.1
- 6.0
- 5.1
-
- 6.1
- 6.0
- 5.1
-
- 6.3
- 6.2
- 6.1
- 6.0
- 5.1
Redistribute HIP Reports
Learn to redistribute HIP reports from GlobalProtect gateways to other firewalls and
Panorama appliances.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
To ensure consistent Host Information Profile (HIP) policy enforcement and to simplify policy
management, you can distribute HIP reports from the GlobalProtect internal or
external gateway to other firewalls, and Panorama appliances in the enterprise. HIP
report redistribution can be useful in the following cases:
- You want to apply consistent policies to both internal and external GlobalProtect gateways.
- You want to apply consistent HIP policies for traffic for a specific user who goes through multiple firewalls.
To redistribute HIP reports, use the same deployment recommendations and best practices that you
use to redistribute User-ID information. Keep in
mind that GlobalProtect internal and external gateways don't support bi-directional
HIP redistribution. Therefore, the best practice is to use your Panorama appliance
as your redistribution point. In this deployment, you would configure your internal
and external gateways to send the HIP reports to Panorama and have Panorama forward
them on to your firewalls for consistent policy enforcement across your
environment.

Use
the following steps to configure HIP report redistribution.
- Configure HIP-Based Policy Enforcement for your gateways and firewalls.Configure HIP report redistribution.
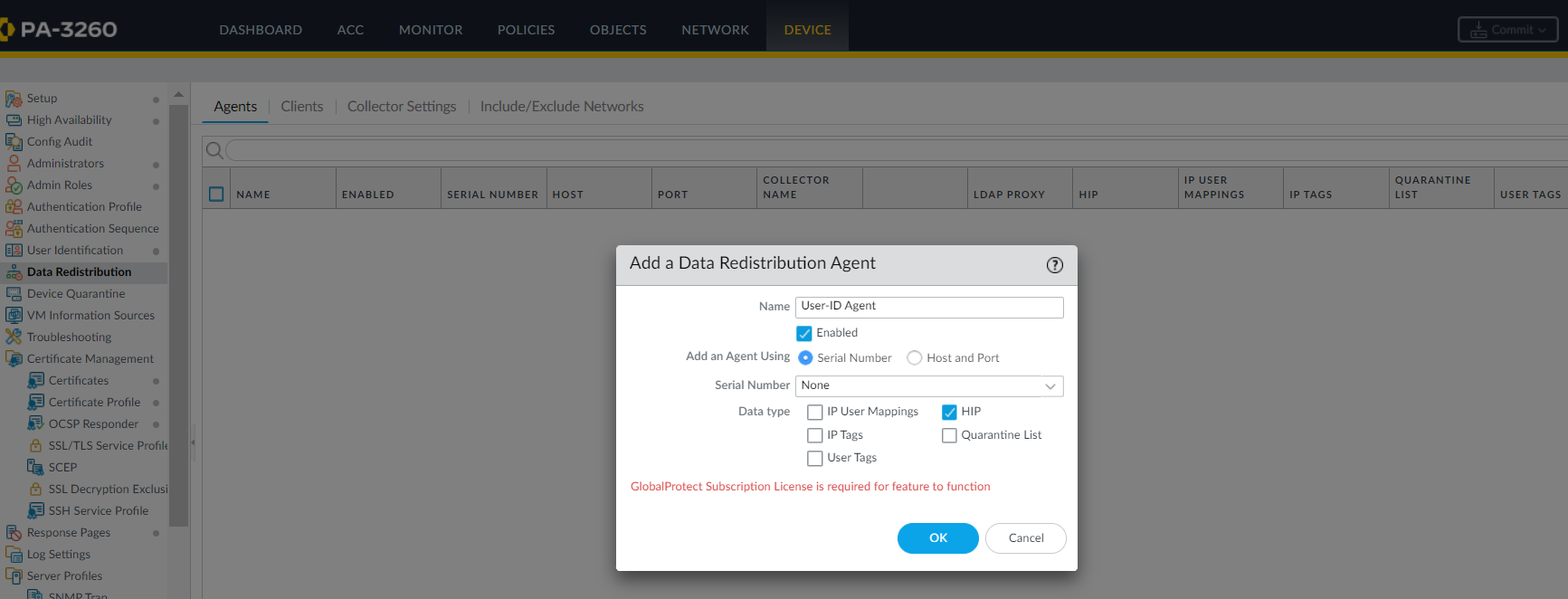
- Select DeviceAgentsData Redistribution.Select an existing or Add a new data redistribution agent.The agent must be a Palo Alto Networks next-generation firewall, a GlobalProtect gateway, or a Panorama appliance.Select HIP Report.
![]() Click OK.If you use GlobalProtect firewalls or gateways to distribute HIP reports, make sure that the group mapping settings on the firewalls or gateways that you use to redistribute the HIP reports match the following attributes on the firewalls or gateways where you have User-ID configured.If you use a Panorama appliance to distribute HIP reports, skip this step.
Click OK.If you use GlobalProtect firewalls or gateways to distribute HIP reports, make sure that the group mapping settings on the firewalls or gateways that you use to redistribute the HIP reports match the following attributes on the firewalls or gateways where you have User-ID configured.If you use a Panorama appliance to distribute HIP reports, skip this step.- Configure the user attributes on the HIP report redistribution firewalls or gateways to match the user attributes on the User-ID firewalls or gateways.For example, if the firewalls or gateways used for HIP report redistribution has a sAMAccountName of Primary attribute and a User Principal Name (UPN) of Alternate Username 1, make sure that you configure the same values on the firewalls or gateways where you have configured User-ID.The attributes don't have to be in the same order; for example, if the HIP report redistribution firewall has a sAMAccountName of Primary attribute and a UPN of Alternate Username 1, you can configure the User-ID firewall with a sAMAccountName of Alternate Username and a UPN of Primary attribute 1.
- If your deployment has user domains configured in its group mapping, configure the user domain attributes on the HIP report redistribution firewalls or gateways to match the user domain attributes on the User-ID firewalls or gateways. User domain attributes must be consistent across all firewalls and gateways.
- Configure the common user groups (the user groups on the firewalls and gateways that connect to the same authentication servers and retrieve the same user groups) on the HIP report redistribution firewalls or gateways to match the user groups on the User-ID firewalls or gateways.