Strata Cloud Manager
Identity Redistribution (Prisma Access)
Table of Contents
Expand All
|
Collapse All
Strata Cloud Manager Docs
Identity Redistribution (Prisma Access)
So that you can enforce your security policy consistently, Prisma Access shares
identity data that GlobalProtect discovers locally across your entire Prisma Access
environment.
So that you can enforce your security policy consistently, Prisma Access shares
identity data that GlobalProtect discovers locally across your entire Prisma Access
environment. Prisma Access can also share identity data with on-premises devices at
remote network sites or service connection sites (HQ and data centers).
For Prisma Access managed by Strata Cloud Manager, we’ve enabled some identity data
redistribution by default, and for what’s left, we’ve made the configuration to
enable redistribution very simple (just select a checkbox to select what data you
want to share).
From the Identity Distribution dashboard, you can see how identity data is being
shared and manage data redistribution (ConfigurationIdentity ServicesIdentity Redistribution.
Identity data that you can redistribute includes:
- HIP data
- IP-address-to-tag mappings
- IP-address-to-user mappings
- User-to-tag mappings
- Quarantined devices
Get started with identity redistribution:
How Identity Redistribution Works
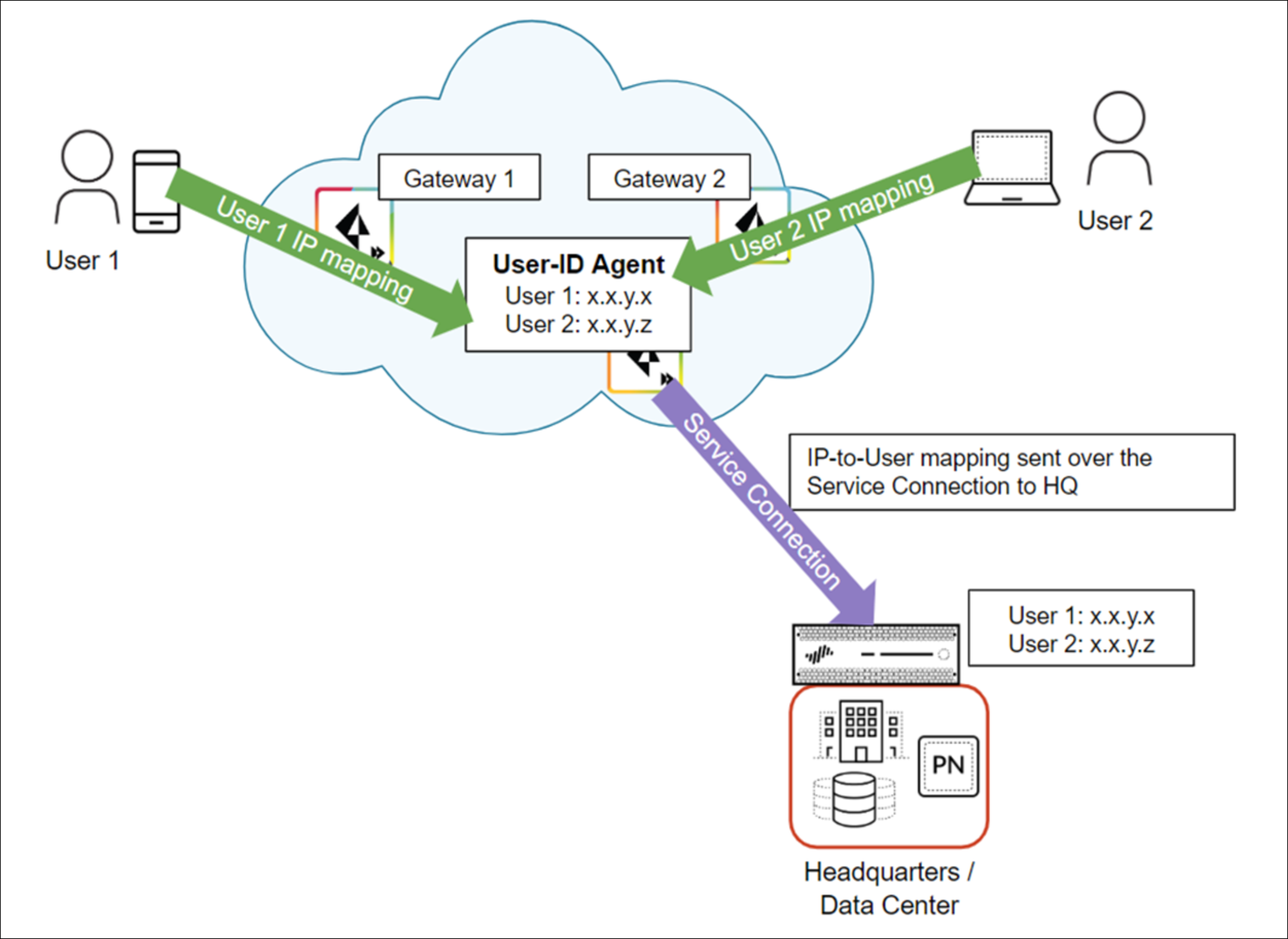
For mobile users to access a resource at a remote network location or HQ/data
center that’s secured by a device with user-based policies, you must
redistribute the identity data from the Prisma Access mobile users and users at
remote networks to that on-premises device.
When the users connect to Prisma Access, Prisma Access collects the user’s
identity data and stores it.
The following example shows two mobile users that have an existing IP
address-to-username mapping in Prisma Access. Prisma Access then redistributes
this mapping by way of a service connection to the on-premises devices that’s
securing the HQ/data center.
Prisma Access managed by Strata Cloud Manager automatically enables service
connections to work as identity redistribution agents (also called User-ID
agents).
Set Up Identity Redistribution
- Confirm Your Service Connection SetupIf you haven’t yet set up a service connection for your HQ or data centers, begin by configuring a service connection. A service connection is required for Prisma Access to share identity data across your environment; Prisma Access automatically enables service connections to work as redistribution agents. A newly-created service connection site will be ready to be used as a redistribution agent when you see that it's been assigned a User-ID Agent Address (Prisma Access does this automatically, and it'll just take a few minutes). Go to ConfigurationIdentity ServicesIdentity Redistribution and set the configuration scope to Service Connections to verify the service connection User-ID agent details.Send Identity Data from Prisma Access to On-Premises DevicesThe service connection’s User-ID agent information is all you need to configure Prisma Access to distribute identity data to on-premises devices.Go to ConfigurationIdentity ServicesIdentity Redistribution and set the configuration scope to Service Connections to get the service connection User-ID agent details.Use these details to configure Prisma Access as a data redistribution agent on Panorama or a next-gen firewall.
![]() Send Identity Data from On-Premises Devices to Prisma AccessAdd on-premises devices to Prisma Access as redistribution agents; the devices you add will be able to distribute identity data to Prisma Access.
Send Identity Data from On-Premises Devices to Prisma AccessAdd on-premises devices to Prisma Access as redistribution agents; the devices you add will be able to distribute identity data to Prisma Access.-
From devices at remote network sites:Go to the Identity Redistribution dashboard, set the configuration scope to Remote Networks, and Add Agent. In addition to specifying the host details, select the type of data the device shares with Prisma Access. Optional settings include the name and a pre-shared key for the device.
![]()
-
From devices at service connection sites:Go to the Identity Redistribution dashboard, set the configuration scope to Service Connections, and Add Agent. In addition to specifying the host details, select the type of data the device shares with Prisma Access. Optional settings include the name and a pre-shared key for the device.
![]()
Configure the Terminal Server Agent for User MappingThe Terminal Server (TS) Agent allocates a port range to each user to identify specific users on Windows-based terminal servers. The TS Agent notifies Prisma Access of the allocated port ranges, so that Prisma Access can enforce policy based on users and user groups.On the Identity Redistribution dashboard, set the configuration scope to Remote Networks, and Add Terminal Server Agent under Terminal Server Sending to Remote Networks Nodes.- By default, the configuration is Enabled.
- Enter a Name for the TS Agent.
- Enter the IP address of the Windows Host on which the TS Agent is installed.
- Enter the Port number on which the agent listens for user mapping requests. The port is set to 5009 by default.
- Save your changes.
![]()
Distribute Identity Data Across Your Prisma Access EnvironmentOn the Identity Redistribution dashboard, Edit the diagram to specify the identity data you want to collect from each source and share across Prisma Access.![]() To activate your changes, push the configuration to Prisma Access.
To activate your changes, push the configuration to Prisma Access.





