Large Multi-Site Deployment with Roaming Agents (With VPN)
Table of Contents
Expand all | Collapse all
-
- Set Up the Endpoint Infrastructure
- Activate Traps Licenses
-
- Endpoint Infrastructure Installation Considerations
- TLS/SSL Encryption for Traps Components
- Configure the MS-SQL Server Database
- Install the Endpoint Security Manager Server Software
- Install the Endpoint Security Manager Console Software
- Manage Proxy Communication with the Endpoint Security Manager
- Load Balance Traffic to ESM Servers
-
- Malware Protection Policy Best Practices
- Malware Protection Flow
- Manage Trusted Signers
-
- Remove an Endpoint from the Health Page
- Install an End-of-Life Traps Agent Version
-
-
- Traps Troubleshooting Resources
- Traps and Endpoint Security Manager Processes
- ESM Tech Support File
-
- Access Cytool
- View the Status of the Agent Using Cytool
- View Processes Currently Protected by Traps Using Cytool
- Manage Logging of Traps Components Using Cytool
- Restore a Quarantined File Using Cytool
- View Statistics for a Protected Process Using Cytool
- View Details About the Traps Local Analysis Module Using Cy...
- View Hash Details About a File Using Cytool
Large Multi-Site Deployment with Roaming Agents (With VPN)
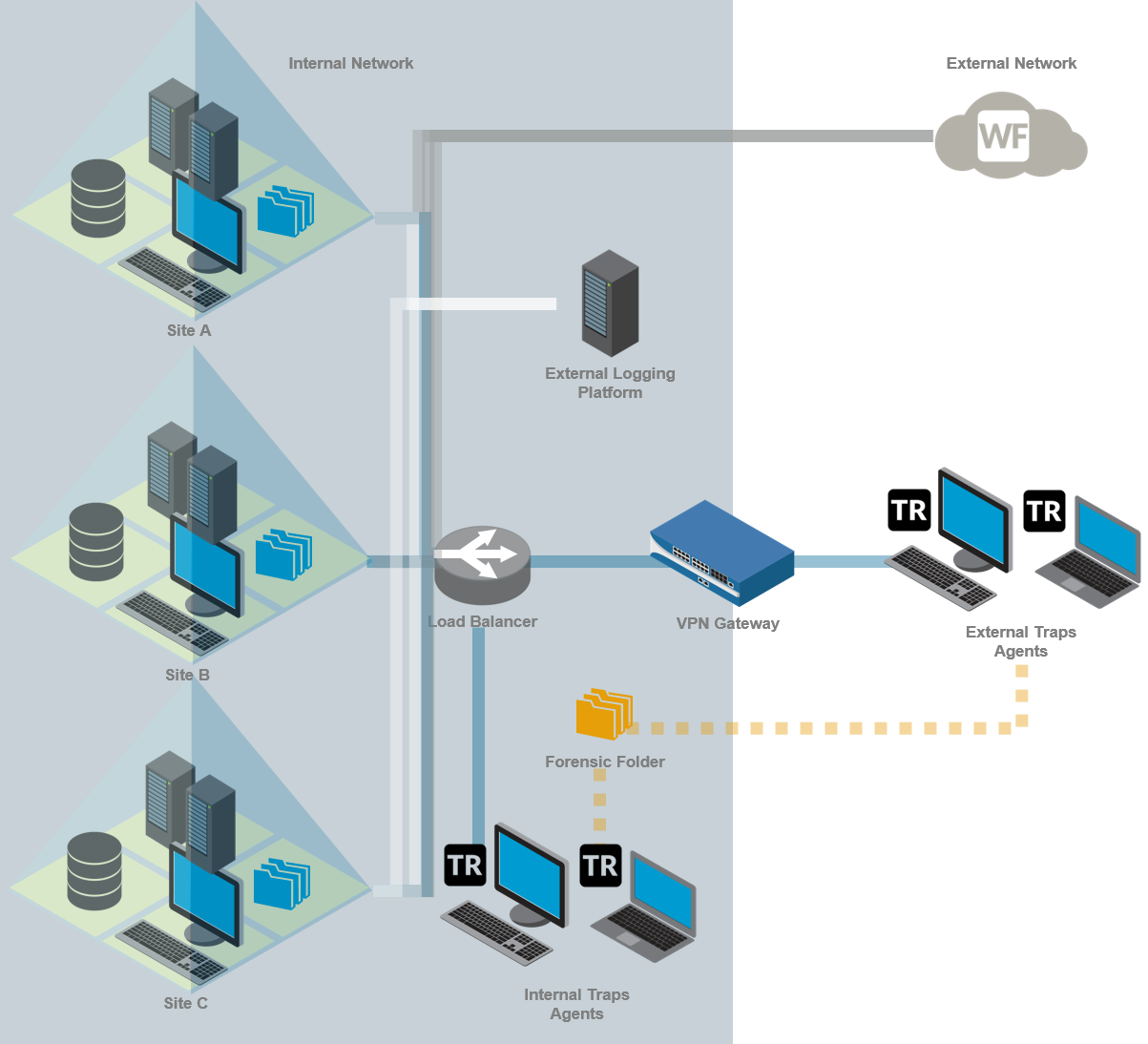
This deployment scenario supports up to 90,000 Traps agents that
can connect through local sites and from off-site locations through
a VPN tunnel. To support up to 150,000 Traps agents, you can deploy
two additional ESM Servers.
This multi-site environment consists of the following components:
- One dedicated database server
- One ESM Console in the same location as the database for managing the security policy and Traps agents
- One ESM Server for every 30,000 Traps agents (for a maximum of 150,000 agents) in each site
- GlobalProtect or an alternative VPN gateway to provide roaming users with an internal IP address for accessing the ESM Server
- One forensic folder for each ESM Server that is accessible by all endpoints for storing real-time forensic details about security events
- (Recommended) WildFire integration
- (Optional) Load balancer for distributing traffic across ESM Servers
- (Optional) External logging platform such as an SIEM or syslog
In this example, Sites A, B, and C each need to support up to
30,000 Traps agents with some of those agents located off-site. To
support this scenario, each site contains an ESM Server that retrieves
the security policy from the database located at Site A. Internal
endpoints connect to the Endpoint Security Manager using their local
ESM Servers. External endpoints connect through a VPN tunnel that
provides the endpoint with an internal IP address for connecting
to the site. If an endpoint is roaming and cannot connect over VPN,
Traps collects prevention data locally until the agent can establish
a connection to the forensic folder.
For additional deployment considerations, see Known
Limitations with Multi-ESM Deployments.
