New Features - Prisma Access - 4.1 Preferred
High-Bandwidth Private App Access with Colo-Connect
Does your organization require high-bandwidth (more than 10 Gbps) access between its network infrastructure and Prisma® Access at multiple locations as part of your hybrid multicloud strategy? Perhaps you’ve thought about aggregating multiple service connections to achieve high bandwidth, but you’re concerned about scalability. If so, Colo-Connect has you covered.
Today, large enterprises are building Colo-based performance hubs to reach private applications in hybrid, multicloud architectures because of the high-bandwidth and low-latency requirements. Typically, these hubs include interconnects to one or more cloud providers and connections to the on-premises data centers over a private or leased WAN. Performance hubs can route traffic between the public cloud and on-premises infrastructure at high speed, and are resilient because of the underlying interconnect infrastructure.
Colo-Connect builds on the Colo-based performance hub concept, offering high-bandwidth (10-20 Gbps) low-latency connections, seamless Layer 2/3 connectivity to Prisma Access from existing performance hubs. This setup limits exposure to the internet and allows the use of private connections for private application connectivity.

Colo-Connect allows you to use Prisma Access to secure private apps using a cloud interconnect that can provide high-bandwidth service connections using the following capabilities:
High bandwidth (up to 20-Gbps) throughput per region for private application access
Support for Dedicated and Partner interconnects using Google Cloud Platform (GCP)
Support for multiple VLAN attachments (up to 20) per interconnect link
Redundant connectivity support per region
New and Remapped Prisma Access Locations and Compute Locations
The following location and compute location changes are made:
- New Compute Locations —The following new compute locations are added, and the following locations are moved to these compute locations:
- Europe North (Stockholm) —The new Sweden location is added to this compute location.
- Middle-East Central (UAE) —The United Arab Emirates location is moved to this location.
- Middle-East Central (Qatar) —The new Qatar location is added to this compute location.
- New Prisma Access Locations —The following new Prisma Access locations are added:
- Sweden
- Kazakhstan
- Qatar
- Senegal
- Remapped Prisma Access Locations —To better optimize performance of Prisma Access, the following locations have been remapped to the following compute locations:
- Ecuador —Remapped from the US Central compute location to the US Southeast compute location
- Jordan —Remapped from the Europe Central compute location to the Europe South compute location
New deployments have the new remapping applied automatically. If you have an existing Prisma Access deployment that uses one of these locations and you want to take advantage of the remapped compute location, follow the procedure to add a new compute location to a deployed Prisma Access location.
Private IP Visibility and Enforcement for Explicit Proxy Traffic Originating from Remote Networks
Some organizations require private IP addresses to skip authentication of headless systems that can't authenticate, set up security policies, and get visibility of the traffic on Prisma® Access Explicit Proxy. You can now accomplish these tasks by leveraging the private IP addresses of the systems in your branch locations that are forwarding traffic to Explicit Proxy using Proxy mode. Proxy mode on remote networks helps to secure outbound internet traffic for users and servers in your branches that need PAC-based connection method due to networking or compliance reasons.
You can enable this functionality when you secure users and devices at a branch with a site-to-site IPSec tunnel using Remote Network and Explicit Proxy Secure Processing Nodes (SPNs).
Service Provider Backbone Integration
Service Providers (SPs) managing tenant connectivity often lack the granular control required to manage egress traffic precisely, forcing reliance on public cloud providers for network backbone and potentially increasing costs or complexity. The Service Provider Backbone Integration feature addresses this by integrating Prisma® Access with a service provider (SP) backbone, which allows you (the SP) to assign specific region and egress internet capabilities to your tenants, providing more granular control over the Prisma Access egress traffic. Without the SP Backbone feature, Prisma Access egress traffic uses public cloud providers for network backbone instead.
This diagram shows Prisma Access egress traffic with SP Backbone integration.

Service Provider Backbone Integration was introduced with Prisma Access 4.1. Starting with Prisma Access version 5.0, you can allow inbound flows to other remote networks over the Service Provider (SP) backbone when you configure the non-inbound access remote network.
Note: SP interconnect supports only the following:
Mobile users, service connections, and remote networks
GCP Regions
New Prisma Access deployments
Explicit proxy egress traffic
Starting March 2024, you can configure, view, and monitor Service Provider IP address pools to leverage your own IP addresses for Prisma Access egress traffic instead of the egress through public cloud providers.
Strata Cloud Manager: Application Name Updates
The application tile names on the hub for Prisma Access, Prisma SD-WAN, and AIOps for NGFW (the premium app only) are now changed to Strata Cloud Manager . With this update, the application URL has also changed to stratacloudmanager.paloaltonetworks.com, and you’ll also now see the Strata Cloud Manager logo on the left navigation pane.
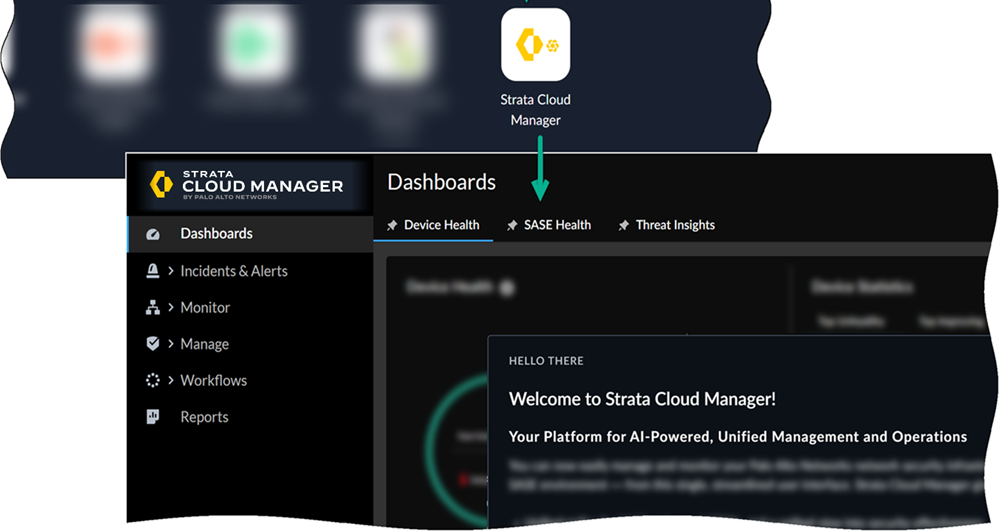
Moving forward, continue using the Strata Cloud Manager app to manage and monitor your deployments.
Third-Party Device-ID in Prisma Access
If your organization has a need to identify third-party devices and apply security policy rules based on that identity, you can use the Cloud Identity Engine along with Prisma® Access to apply information from third-party IoT detection sources to simplify the task of identifying and closing security gaps for devices in your network. This API-driven integration automatically simplifies security enforcement by leveraging information from third-party IoT visibility solutions via the Cloud Identity Engine, ensuring comprehensive device visibility and control by using Prisma Access security policy rules that are robust and context-aware.
Traffic Replication and PCAP Support
Prisma® Access secures your traffic in real time based on traffic inspection, threat analysis, and security policies. While you can view Prisma Access logs to view security events, your organization might have a requirement to save packet capture (PCAP) files for forensic and analytical purposes, for example:
You need to examine your traffic using industry-specific or privately-developed monitoring and threat tools in your organization and those tools require PCAPs for additional content inspection, threat monitoring, and troubleshooting.
After an intrusion attempt or the detection of a new zero-day threat, you need to preserve and collect PCAPs for forensic analysis both before and after the attempt. After you analyze the PCAPs and determine the root cause of the intrusion event, you could then create a new policy or implement a new security posture.
- Your organization needs to download and archive PCAPs for a specific period of time and retrieve as needed for legal or compliance requirements.
- Your organization requires PCAPs for network-level troubleshooting (for example, your networking team requires data at a packet level to debug application performance or other network issues).
To accomplish these objectives, you can enable traffic replication which uses the Prisma Access cloud to replicate traffic and encrypt PCAP files using your organization's encryption certificates.
Transparent SafeSearch Support
Prisma Access allows you to resolve search engine queries from mobile users and users at remote networks to the engine's SafeSearch portal by performing an FQDN-to-IP mapping. This functionality can be useful if you have guest internet services at your organization and you want your guests to safely use search engines, preventing them from searching for potentially inappropriate or offensive material that could be against company policy.
